This guide will demonstrate how to setup users on a Linux instance on a Mac/Linux machine and how to create SSH Keys for those users.
“User Setup” will provide instructions on how to add and delete users, as well as assigning sudo privileges. Sudo will provide users administrative privileges.
“SSH Keys” provide a secure way of logging into servers and are recommended for all users. Configuring SSH-key-based authentication to your server allows users to sign in without providing an account password.
CentOS 7: User Setup
Create User
Connect to your server. Instructions on how to connect can be found here: SSH to Instance using Mac and Linux
Create new user, in this example name them newuser, and give user a password with the following commands:
sudo adduser newuser
sudo passwd newuser |
Assigning Sudo Permissions [Optional]
To give the user sudo permissions, add the user to the group wheel, which gives sudo access to all members.
sudo gpasswd -a newuser wheel |
The function lid shows which groups a user belongs to. Using function lid with -g flag will show which users belong in the indicated group.
The following will show the usernames of those in the group wheel.
To remove sudo permission, remove user from group wheel.
sudo gpasswd -d newuser wheel |
Delete User
If there is a user account no longer needed, run the following to delete the user without deleting their files:
To delete the user’s home directory and account, run this instead:
Both commands will automatically remove users from all added groups.
CentOS 8: User Setup
Create User
Connect to your server. Instructions on how to connect can be found here: SSH to Instance using Mac and Linux
Create new user, in this example name them newuser, and give user a password with the following commands:
sudo adduser newuser
sudo passwd newuser |
Assigning Sudo Permissions [Optional]
To give the user sudo permissions, add the user to the group wheel, which gives sudo access to all its members.
sudo usermod -aG wheel newuser |
The function lid shows which groups a user belongs to. Using function lid with -g flag will show which users belong in the indicated group.
The following will show the usernames of those in the group wheel.
To remove sudo permission, remove user from group wheel.
sudo gpasswd -d newuser wheel |
Delete User
If there is a user account no longer needed, run the following to delete the user without deleting their files:
To delete the user’s home directory and account, run this instead:
Both commands will automatically remove users from all added groups.
Ubuntu: User Setup
Create User
Connect to your server. Instructions on how to connect can be found here: SSH to Instance using Mac and Linux
Create new user, in this example name them newuser, with the following commands:
This command will also ask to:
Assign and confirm a password for the new user
Enter any additional information about the new user. This is optional and can be skipped by pressingENTER.
Enter Y to confirm the information and continue.
Assigning Sudo Permissions [Optional]
To give the user sudo permissions, add the user to the group sudo, which gives sudo access to all members.
sudo usermod -aG sudo newuser |
The following will show the usernames of those in the group sudo.
To remove sudo permission, remove user from group wheel.
sudo gpasswd -d newuser sudo |
Delete User
If there is a user account no longer needed, run the following to delete the user without deleting their files:
To delete the user’s home directory and account, run this instead:
sudo deluser --remove-home newuser |
Both commands will automatically remove users from all added groups.
Allow Password Authentication
As the root user, run sudo vi /etc/ssh/sshd_config.
Tap the i or insert key on your keyboard and edit the lines:
PasswordAuthentication no to PasswordAuthentication yes
Save and exit the vi file by typing Esc, :, w, q, and Enter.
Restart the service: sudo systemctl restart sshd
SSH Key (CentOS 7, CentOS 8, & Ubuntu)
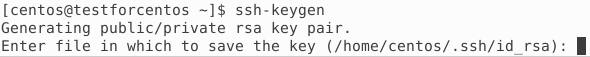
Open a terminal window.
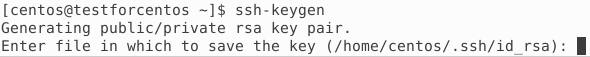
Create a key pair.
The following prompt will appear, click Enter to save in the home directory.
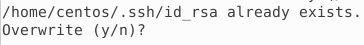
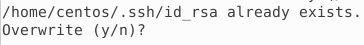
If you previously generated a SSH key pair, it may ask you to overwrite it. Be careful when selecting yes. You will not be able to authenticate the previous key and it cannot be reversed.
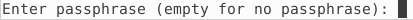
Enter a passphrase as desired. Then press Enter.
Copy your public key, specifying which user account you have SSH password access to and the IP address.
ssh-copy-id newuser@ipaddress |
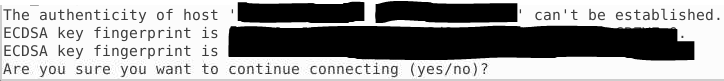
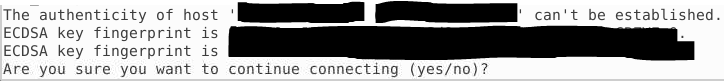
If the following prompt appears, type Yes. This prompt is a result of connecting to the host for the first time.
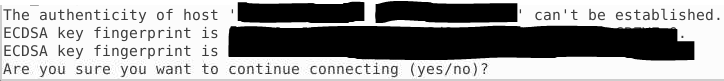
Enter the user’s password when prompted.
Skip to Step 5 if successful.
If prompted an error, please double check Allow-Password-Authentication was completed.
If you are not able to use ssh-copy-id, an alternative is the following command. Remember to replace newuser and ipaddress.
cat ~/.ssh/id_rsa.pub | ssh newuser@ipaddress "mkdir -p ~/.ssh && touch ~/.ssh/authorized_keys && chmod -R go= ~/.ssh && cat >> ~/.ssh/authorized_keys" |
Similarly, if the following prompt appears, type Yes. This prompt is a result of connecting to the host for the first time.
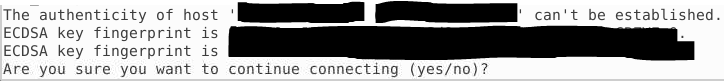
Enter the user’s password when prompted.
If prompted an error, please double check Allow-Password-Authentication was completed.
Exit and reopen the terminal.
Connect to the server with the following, where newuser should be replaced with the appropriate user and ipaddress with the IP address of the remote host.
[Optional] Once key-based logins are working, you can decide to disable username and password logins for better security.
Edit server’s configuration file.
sudo vi /etc/ssh/sshd_config |
Tap the i or insert key on your keyboard and edit the lines, referenced below:
[...]
PasswordAuthentication no
[...]
UsePAM no
[...]
|
To save, press esc, :, w, q, Enter.
Reload the server’s configuration.
sudo systemctl restart sshd.service |